Some might think that by offering a bounty program, for what is often considered the world’s most secure operating system, that action would quickly get taken for finds. This does not appear to be the case for, at least, one man’s discoveries. It does, unfortunately, show a pattern for the Cupertino company to leave some exploits unpatched long after being notified about them. App developer Jeff Johnson recently posted on his blog about an exploit he discovered in September of 2019. His blog goes into detail about how the exploit functions.
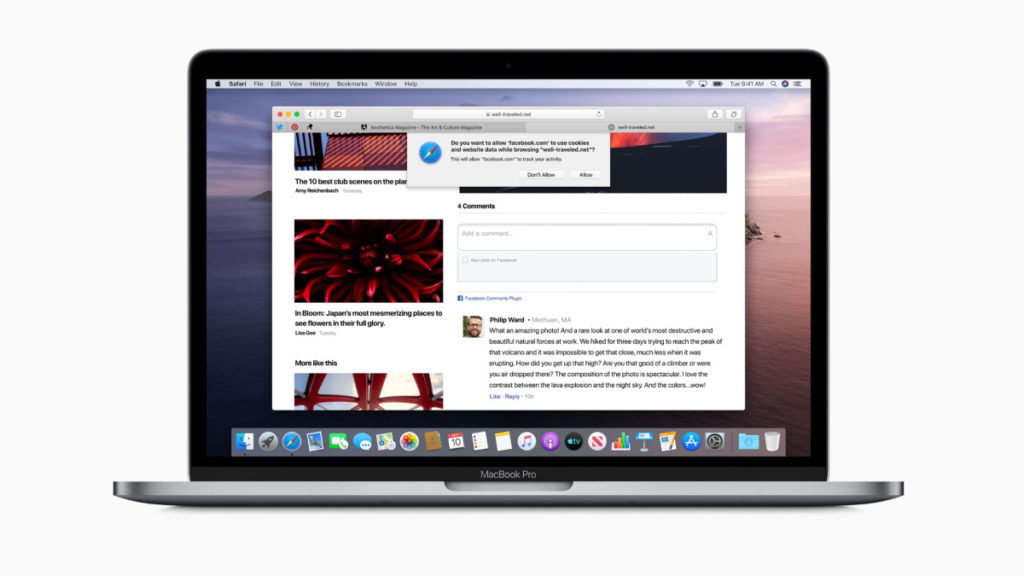
Today I’m disclosing a macOS privacy protections bypass. (You may recall that I disclosed another one last year.) The privacy protections system (also known as TCC: Transparency, Consent, and Control) was introduced in macOS Mojave, and one of its purposes is to protect certain files on your Mac from access by unauthorized apps. I’ve discovered a way for an unauthorized app to read the contents of protected files, thus bypassing the privacy protections. This issue exists in Mojave, Catalina, and the Big Sur beta. It remains unaddressed and is, therefore, in one sense, a zero-day.
He goes on to produce a timeline illuminating on a long, drawn-out process of reporting and following up on the exploit. It starts with reporting to Apple’s security bounty program, and Apple Product Security, on December 19th, 2019. Nearly a month later, he’s told that they hope to address it in the spring of 2020. Come spring, and after multiple update inquiries, he’s told they are still investigating it. This is even after the recent Big Sur beta is released. A day after being told that it’s still under investigation, on June 29th, he goes public with it.
Not the first discovery
This is not the first exploit he’s discovered either. The Register reports he discovered another in February 2019 that was still not fixed eight months after notifying Apple. It too is similar to this latest find, that one could also allow unauthorized access to directories containing sensitive user data. Upon following up on it, last October, he’d been informed it still had not been fixed. Perhaps Apple is merely waiting to fix these as it transitions away from Intel? This could be the case if some hardware-level detail is playing a factor in the exploit.
