An electrical engineer named Joe Grand managed to recover $2 million dollars worth of bitcoin from a Trezor One crypto wallet after its owner had lost the PIN for the device. Dan Reich had originally stored $50,000 on it in 2018. The type of bitcoin used is called Theta, and in 2021, its value reached an all-time high of $15 per token. That was when his investment value had more than quadrupled, and he sought to withdraw it before the price dropped again and corrected itself. However, he had forgotten the PIN, and after 12 guesses, he was approaching the 16-try limit before the wallet automatically erased itself.
Lucky for him, he was able to work with someone who has quite a bit of experience in hardware hacking. Mr. Grand has an extensive resume in such matters that also includes testifying before the U.S. Congress as part of the famed L0pht hacker collective about a serious vulnerability that could not only potentially take down the internet but even intercept and redirect information for intelligence agencies. With such credentials one, would think hacking what is essentially a flash drive with a PIN code would be easy, right? Well, not necessarily so.
“I was contacted to hack a Trezor One hardware wallet and recover $2 million worth of cryptocurrency (in the form of THETA). Knowing that existing research was already out there for this device, it seemed like it would be a slam dunk. Little did I realize the project would turn into a roller coaster ride with over three months of experimentation, failures, successes, and heart-stopping moments. It reminded me that hacking is always unpredictable, exciting, and educational, no matter how long you’ve been doing it. In this case, the stakes were higher than normal: I only had one chance to get it right.”
Ultimately what had given Joe and Dan hope in achieving their goal was a 2018 conference talk in which engineers from overseas explained a potential exploit for the Trezor One crypto wallet. Dan had reached out to them, and his request for assistance was declined. With so much on the line, he was not willing to give up and was able to contact a financier in France who said they could get the drive to associates in Switzerland that would remain unnamed, and it would involve an almost James Bondesque handing-off of the wallet.
Just as Dan had begun to consider making the trip and its questionable details, he’d started researching Mr. Grand’s history. As a fellow engineer and owner of a software company, he contacted Mr. Grand and, soon thereafter, realized he had the right person.
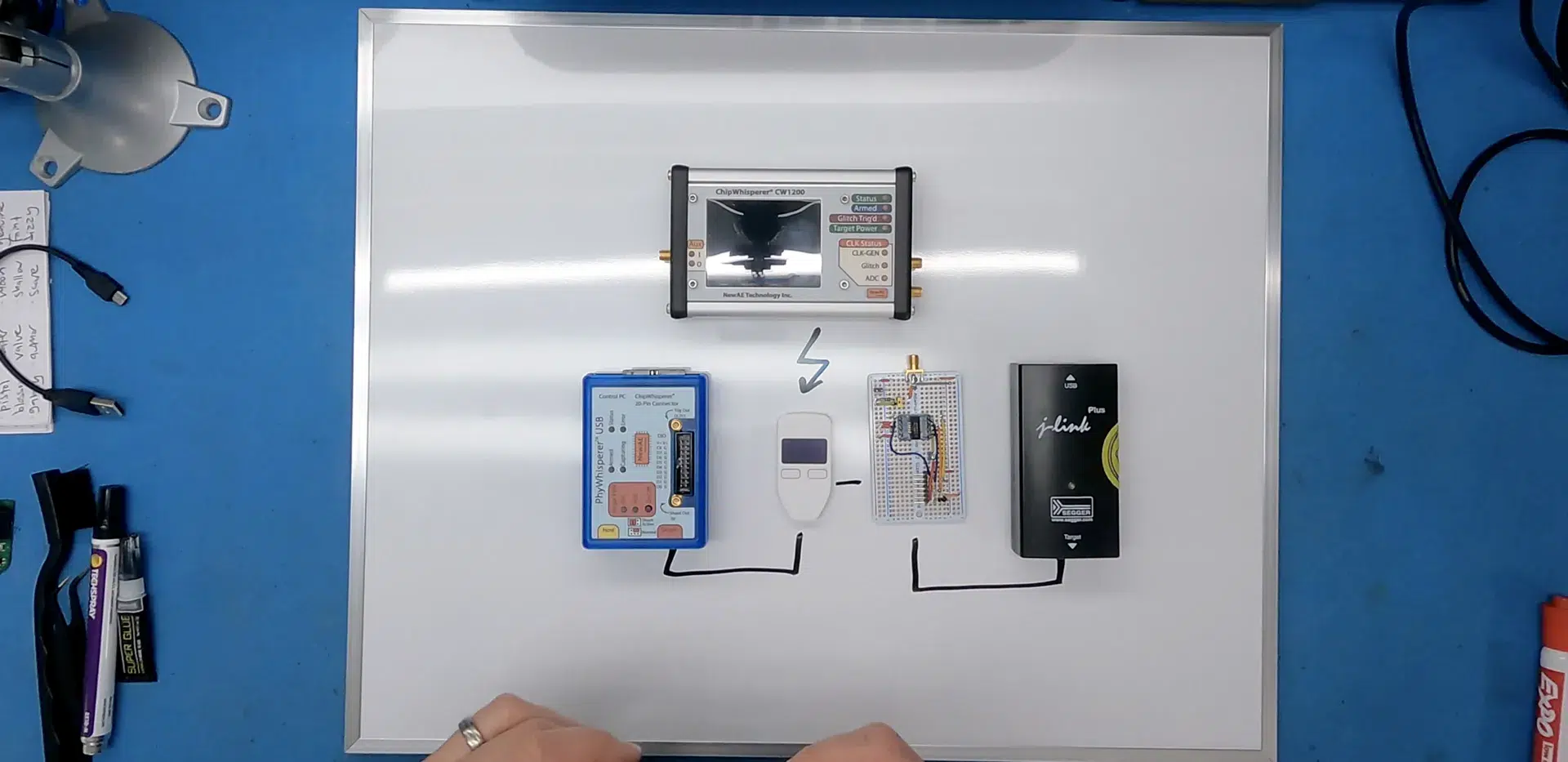
Simply put, the exploit(s) for getting the wallet to release its booty revolved around another previously discovered by a 15-year-old in the U.K. back in 2017. That person had helped another recover roughly $30,000, small fry compared to this latest lost treasure. The trick involved finding where the PIN had been stored in RAM after a firmware update that allowed unauthorized code to be installed. The method was not without risks, as it could inadvertently cause the RAM to erase itself. This led the two to look at the research done in 2018. They discovered that the wallet would still temporarily move the PIN to RAM to prevent it from being erased during updating. The solution was a type of fault injection attack to read the PIN before it was removed. The risk was still high, as this could be a one-shot, and if it failed, the PIN would be lost forever.
Lucky for them, it worked, and Dan did pay Joe a percentage of the recovered funds as compensation for his hard work. Trezor has also published a statement that this exploit has since been patched out in another firmware update.
“Hi, we just want to add that this is an outdated exploit that is not a concern for current users and that we fixed in 2017 right after a report that we received through our responsible disclosure program. This attack requires full physical access to the device, and there is no record of any funds being compromised.”