
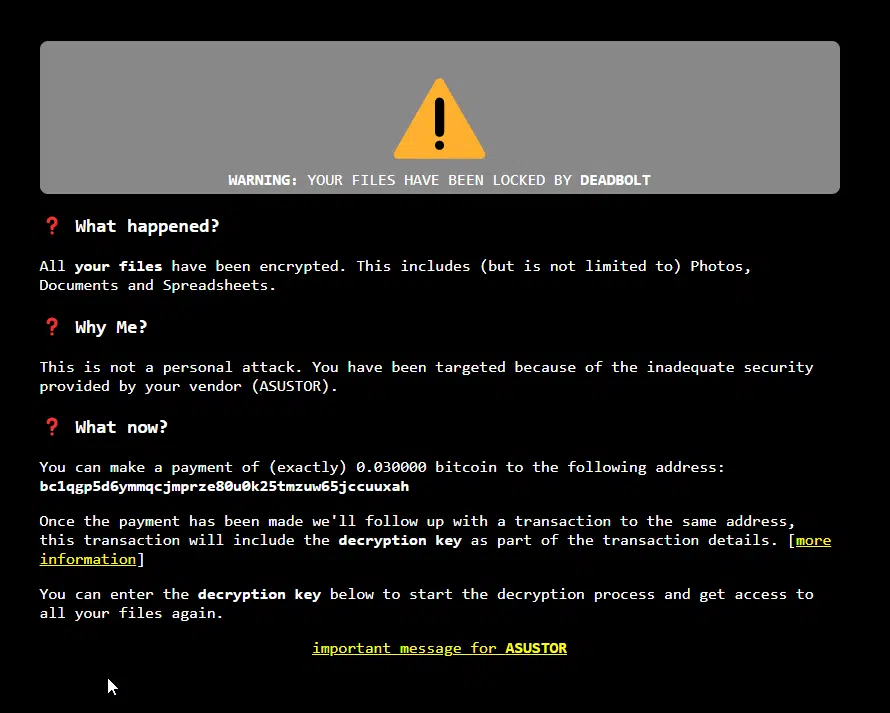
Following earlier coverage relating to QNAP devices, the dreaded DeadBolt ransomware has now begun proliferating on NAS units manufactured by Asustor, according to increasing posts on reddit and the company’s own community forum from users who were surprised to find that all of their files have been encrypted. Owners of Asustor’s NAS devices have been advised to disconnect their units from the internet immediately, lest they wish to lose file access and be greeted with a ransom message seeking .03 BTC (around $1,140 at the time of this posting) in order to have their content unlocked. Users may also want to desynchronize from cloud services, as some DeadBolt victims inadvertently ended up pushing their encrypted files to services such as OneDrive and Google Drive as well.
Ransomware Attack – Megathread (r/asustor)
- In response to Deadbolt ransomware attacks affecting ASUSTOR devices, the myasustor.com DDNS service will be disabled as the issue is investigated. ASUSTOR will release more information with new developments as we investigate and review the causes to ensure this does not happen again. We remain committed to helping affected customers in every way possible.For your protection, we recommend the following measures:
- Change default ports, including the default NAS web access ports of 8000 and 8001 as well as remote web access ports of 80 and 443.
- Disable EZ Connect.
- Make an immediate backup.
- Turn off Terminal/SSH and SFTP services.
- For more detailed instructions on protecting your security, please refer to the following link: https://www.asustor.com/en-gb/online/College_topic?topic=353. If you find that your NAS has been affected by Deadbolt ransomware, please follow the steps listed below.
- Unplug the Ethernet network cable
- Safely shut down your NAS by pressing and holding the power button for three seconds.
- Do not initialize your NAS as this will erase your data.
- Click on the link for more information and instructions to contact ASUSTOR for help with recovery: https://www.asustor.com/en-gb/knowledge/detail/?id=&group_id=628
Deadbolt Ransomware Attacks Target ASUStor NAS (Tom’s Hardware)
- DeadBolt has been in the wild for some time now, infecting unprotected NAS systems connected to the Internet. The same ransomware previously wreaked havoc on QNAP devices, and it would appear that Asustor was the next target.
- The perpetrators are asking for 0.03 bitcoin, which by today’s exchange rate is around $1,154. It’s the same sum that the hijackers had demanded from their QNAP victims. Surprisingly, the gang didn’t make Asustor any offers. With QNAP, the group had offered to share the vulnerability details with the company for five bitcoins ($184,000) or sell it the universal decryption master key for 50 bitcoins ($1.85 million).
- It’s unknown if all Asustor NAS devices are susceptible to the DeadBolt attack as there is user feedback that some models, such as the AS6602T, AS-6210T-4K, AS5304T, AS6102T, or AS5304T, are free of infection. Meanwhile, some affected models include the AS5304T, AS6404T, AS5104T, and AS7004T.
